

Computer repair, sales and upgrades. We offer a variety of services and items. Mobile & Remote Support for Mac & PC's. If your Mac or PC is giving you the blues call Blue Mountain Computers today.
Some upgrade options are available for your older Macs & PC's. Why buy new, when Blue Mountain Computers can recondition most Macs and PC's and get them running like new again. Call us for details to talk about your options.
We buy Macs dead or alive and some laptops.

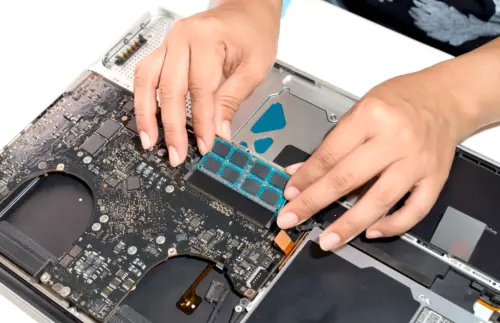
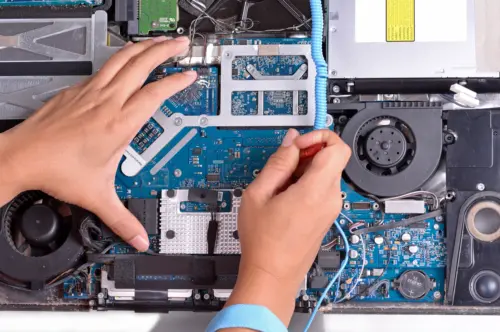
Blue Mountain Computers specializes in Mac and PC upgrades. Quality parts installed and replaced to give you ultimate performance in your computer. Factory replacement parts and other manufacturer high performance parts are available.
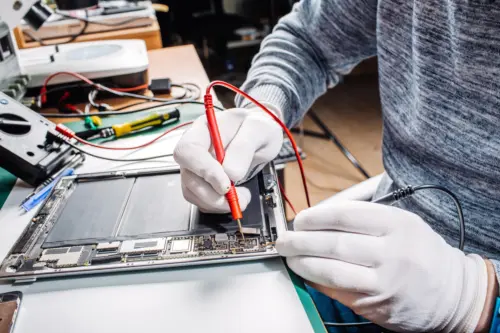
We offer computer repairs for Mac and PC. Professional Setups, testing, and diagnosis to determine your computer's repair needs. Accurate repair techniques to ensure your computer is operating properly again.

We buy and sell Macs and some PC laptops. Whether you are looking for a new or used computer, we can help you purchase the right unit you need. Call us for more information and we will be glad to assist with your needs.

Here are reviews provided by some of our customers on Google. Thank all of you so much!
Blue Mountain Computers-
We have used Blue Mtn ever since we moved to Hendersonville 13 years ago and the service has been excellent. We had a pc till a couple of years ago when Glenn converted us to a MAC. Now that he does all remote work it has been such a benefit not to need to take the equipment to the shop for analysis and fixing. Blue Mtn is tops and we would be lost without them.
After being scammed by a bogus "Apple Services " outfit for servicing our IMAC, Blue Mt. completely cleaned up and restored our computer. It took awhile mainly because of the time required and the fact that they are in such high demand but thankfully all is well.Glenn was very thorough both in the work and explanation of the tasks that were accomplished. The fee was very reasonable considering the amount of time that was required. Very grateful!!
Absolutely fantastic! Hands down the best computer repair shop around, and I've used a few... It was such a pleasure working with Glenn. He communicates extremely well, is reasonably quick, fair priced and very, very friendly.The art of treating your customers as you would like to be treated has not been lost on Glenn. I had a horrifically labor intensive recovery on a crashed hard drive for my business computer. There were a lot of important files on the drive that I could not afford to loose, which is what I feared would be the case. With Glenn's knowledge and expertise, he was able to recover all the data I needed and really saved my butt! No more Geek Squad surly attitudes and waiting for weeks and weeks and weeks to get my computer back. Blue mountain computers is the only shop I will ever use. They have EARNED my business. Glenn, you are the MAN! Thank You!
Glenn and his wife did a fantastic job repairing my MacBook. Very easy to work with, fair prices, and great communication throughout the whole process. 10/10 recommend!
Glenn was extremely easy to work with and very efficient on speeding up my computer, faster than it was when it was new. I’m an an extremely happy customer. Totally recommend his services.
Glenn and Amy are absolutely amazing! I had a Mac that was acting up and made an appointment to have Glenn look at it. Right away he let me know what was wrong with it and how much it would be to fix it, however he also offered me the option to trade it in for an upgrade. I decided to upgrade. They worked quickly and communicated with me throughout the entire process. They transferred all my data onto my new one, and set it up with everything I needed. I couldn’t be happier with my upgrade and with the process. I highly recommend Blue Mountain Computers for any of your Mac needs, whether it’s a clean-up, improvements on the system, or a trade-in for upgrade. If you’ve got a Mac, these are the people who you need taking care of it. They are honest, reliable, very knowledgeable, and they will take care of you.
I have had used Blue Mtn computers two times now and have had EXCEPTIONAL service. Glen helped us extract content off of the hard drive of an old PC computer. He did a great job, his prices were fair and was straightforward about the turnaround time.
He also worked on my mac book which needed help with storage issues, time machine back-ups and software updates. He spent time with me and carefully explained what needed to happen. He was clear, his prices were fair and he addressed the issue in a timely manner. Being in grad school and using my computer daily made his support a real lifesaver.
I would completely recommend Blue Mountain! Thank you!
I have been. using Blue Mountain Computer for several years. They have repaired 3 Macs and one PC notebook. Always made my computers work better than before and they stayed fixed. They tune me up for speed remotely on occasion. Really capable and honest people. I am very thankful they are here. Jim
What is adware?
Adware is any software application that has the ability to display advertisements on your computer. Some adware may track your Web surfing habits. These advertisements may be displayed in many forms, including, but not limited to, pop-up, pop-under, and banner advertisements. Adware may slow your Web browser’s performance. Worst case scenario: Some adware may have the ability to download third party software programs on your computer without your knowledge or consent.
What is a cookie (or Adware Cookie)?
Cookies are pieces of information that are generated by a Web server and stored on your computer for future access. Cookies were originally implemented to allow you to customize your Web experience. However, some Web sites now issue adware cookies, which allow multiple Web sites to store and access cookies that may contain personal information (surfing habits, usernames and passwords, areas of interest, etc.), and then simultaneously share the information with other Websites. Adware cookies are installed and accessed without your knowledge or consent. Worst case scenario: This sharing of information allows marketing firms to create a user profile based on your personal information and sell it to other firms.
What is a keylogger?
A keylogger is a type of system monitor that has the ability to record all keystrokes on your computer. Therefore, a keylogger can record and log your e-mail conversations, chat room conversations, instant messages, and any other typed material. They have the ability to run in the background, hiding their presence. Worst case scenario: A third party may be able to view your personal conversations and may gain access to private information such as your usernames, passwords, credit card numbers, or your Social Security number.
What is a virus?
A program or code that replicates, that is infects another program, boot sector, partition sector or document that supports macros by inserting itself or attaching itself to that medium. Most viruses just replicate, many also do damage.
What is a worm?
A worm is a program that replicates itself over a computer network and usually performs malicious actions, such as using up the computer's resources and possibly shutting the system down. The name is an acronym for "write once, read many." A recent example of a worm is the Sasser worm (or W32.Sasser.A and its variants) that affected millions of corporate and private computer systems. Earlier in 2004, the Netsky worm (or W32/Netsky) spread by mass email using addresses obtained from an infected computer. It also spreads via local networks by trying to copy itself to shared folders on drives C: to Z:.
What is a Trojan horse (also known as Trojan or Backdoor Trojan)?
A Trojan horse is a program that allows a hacker to make changes to your computer. Unlike a virus, a Trojan does not replicate itself. It is generally disguised as a harmless software program and distributed as an e-mail attachment. Once you open the attachment, the Trojan may install itself on your computer without your knowledge or consent. It has the ability to manage files on your computer, including creating, deleting, renaming, viewing, or transferring files to or from your computer. It may utilize a program manager that allows a hacker to install, execute, open, or close software programs. The hacker may have the ability to open and close your CD-ROM drive, gain control of your cursor and keyboard, and may even send spam by sending mass e-mails from your infected computer. They have the ability to run in the background, hiding their presence. Worst case scenario: A third party may gain access to your computer and do whatever the author has designed it to do.
What is "Remove me"?
“Remove Me” are options on spam that are often fake. That is, if you respond to request removal, you very well may be subjecting yourself to more spam, because by responding, the sender knows that your email account is active. A 2002 study performed by the FTC demonstrated that in 63% of the cases where a spam offered a "remove me" option, responding either did nothing or resulted in more email. What is shareware?Software distributed for evaluation without cost, but that requires payment to the author for full rights. If, after trying the software, you do not intend to use it, you simply delete it. Using unregistered shareware beyond the evaluation period is pirating.
What is spyware?
Spyware is software that sends information about your Web surfing habits to its Web site. Often quickly installed in your computer in combination with a free download you purposely selected from the Web, spyware transmits information in the background as you move around the Web. Also known as "parasite software," "scumware," "junkware" and "thiefware, spyware is occasionally installed just by visiting a Web site (see drive-by download). The license agreement that everyone accepts without reading may or may not divulge what the spyware does. For example, it might say that the program performs anonymous profiling, which means that your habits are being recorded, not you individually. Such software is used to create marketing profiles; for example, people who go to Web site "A" often go to site "B" and so on. Spyware may deliver competing products in realtime. For example, if you go to a Web page and look for a minivan, an ad for a competitor's vehicle might pop up (see adware). Merchants place ads with spyware advertisers because they feel their promotions are focused. In fact, many feel that the Internet has opened up the most intelligent marketing system the world has ever seen. Merchants say they are targeting prospects who are really interested in their products, and spyware vendors argue that as long as they treat users anonymously, they are not violating privacy. There are also spyware programs that keep changing the home page in the browser to a particular Web site or just keep popping up their ads all the time. Nevertheless, once you detect spyware, it can be eliminated, albeit sometimes with much difficulty. The downside is that people become suspect of every piece of software they install, and some even go so far as to "read the dreaded software license.
What is a browser hijacker?
Browser hijackers have the ability to change your Internet Explorer settings, redirect your Web searches through their own search engines, redirect mistyped or incomplete URLs, and change your default home page. They may redirect your searches to “pay-per-search” Websites which are very often pornographic Website. Worst case scenario: If a hijacker changes your Internet Explorer browser settings, you may be unable to change back to your preferred settings. You may also be unable to browse the Internet entirely.
Viruses
Programs executed on the 'infected' machine with malicious intent. Viruses contain self-preservation mechanisms (such as 'infecting other executables') but usually need user intervention to propagate (for example, a user needs to open an attachment) Worms—Self-Replicating Viruses that propagate automatically without any user intervention (for example, using a Buffer Overflow vulnerability present on an exposed service) Backdoors—Programs that allow the malicious attacker remote access to the 'infected' machine without requiring normal user authentication and authorization Trojans—Programs that contain a benign functionality (for example, a game) and a malign feature (for example, a backdoor). As in the original story, a Trojan program is designed in such a way that it bypasses normal defences and is knowledgeably executed by the user User-Level RootKits—Programs that 'infect' program files that are executed by the user and run under the user account's privileges (for example, the Explorer.exe or Word.exe program) Kernel-Level RootKits—Programs that 'infect' functions belonging to the Operating System kernel (i.e. the core Windows operating system) and are used by hundreds of applications (including the Windows API). Kernel-Mode RootKits will modify (i.e. hijack) internal operating system functions that return lists of files, processes, and open ports (use the 'DependencyWalker' program to see Kernel functions on the 'NTDLL.dll', 'Kerner32.dll', and 'NTOSKRNEL.exe' files) For example, in an infected machine, although the RootKit program is active and running in its own process, the 'Task Manager' won't show it because 'Task Manager' relies on Windows Kernel functions to retrieve the list of running Processes (that can be changed so that the results won't include the RootKit's own process). For an extended and well-presented explanation of these Malware programs, I strongly recommend the Ed Skoudis book Malware: Fighting Malicious Code (ISBN: 0-13-101405-6). There are several ways in which these Malware programs can be propagated: Infecting executables with the Malware code.Exploiting known vulnerabilities (for example, buffer overflows).E-mailing itself to the victim's entire contact list.Infecting an application's source code with the Malware code.A V.W.T.B.R.M. (Virus.Worm.Trojan.Backdoor.RootKit.Malware).
What is privacy?
Privacy is the interest that individuals have in sustaining a 'personal space,' free from interference by other people and organizations.
As many of you are aware, the building location we were in at 1534 Haywood Road for almost 10 years is being sold.
As of March 1st 2022, we went to a full remote and mobile business model. If you need any Apple or PC help or repair our number is 828-692-4689 or Glenn’s mobile number is 828-424-0258 and his email address glenn@bluemtncomputers.com will remain the same.
If we can assist you remotely, we will and if not, we can schedule a service call or even a pickup and then a delivery and setup once your Mac or PC is repaired.
You can message Glenn at 828-424-0258, email him or call us with any questions.
As always thank you for being part of our family for the last 21 years and working with us as we transition to our new phase in the business to better assist all of our amazing customers.
Give Us a Call
Phone:
Office: 828-692-4689
Mobile: 828-424-0258
Email:
glenn@bluemtncomputers.com

Phone:
828-692-4689
828-424-0258
Email:
glenn@
bluemtncomputers.com
Hendersonville, NC